I’m UNIX guy and loves ssh to connect other servers, but I have to configure ssh-tunneling every time when I want to use other port than 22/tcp. SSH-tunneling is suit for me in some view. SSH-tunneling can go through SOCKS proxy, but this work is very little thing but just a little bit stressful for me. There is some limitation about ssh-tunneling. Some protocol such as Windows file sharing needs UDP and ssh-tunneling cannot treat with it. Your underling network configuration is bound by your local network, so you cannot resolve your home server’s host name using your home DNS server. So, I’ve tried to dig external network to my home network using OpenVPN.
1. Overview
OpenVPN is a little difficult to think about.
- OpenVPN allows several style of connection such as point-to-point and access server(one server-to-many client). I’ve chosen access server style configuration. Under this configuration, One access server wait for connection from client. When connection established, server acts as gateway to your home network.
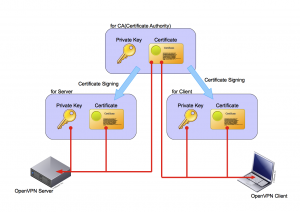
- OpenVPN uses SSL, so you have to setup several certificate which is need to establish SSL network connection.
- OpenVPN allows several authentification when you are going to establish VPN connection. password authentication, certificate authentification, and both of them.
OpenVPN also has many many feature. If you want to know what OpenVPN can do, please refer ["What is OpenVPN?" page](http://openvpn.net/index.php/open-source/333-what-is-openvpn.html).
2. Big Picture for test
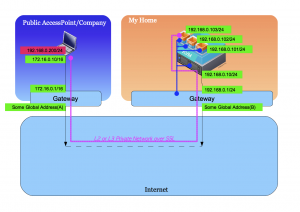
So, I’m going to try to deploy testing environment. Here is big-picture about testing environment.
You can see one server in “My Home” area. This server is virtualized with kvm and software switch using bridge-utils. There are three virtual server on one physical server and one virtual server of thee is OpenVPN server. “My Home” LAN and WAN is separated with gateway and access from external network is limited, but I’ve set that (B):1194/udp goes directly to 192.168.0.103:1194/udp and vice versa.
Also you can see one notebook in “Public Access/Company” area. This notebook is Windows and I’ve installed OpenVPN client, some certificate and keys. When this notebook try to connect to “My Home”’s OpenVPN server, this notebook is going to connect to (B):1194/udp. When negotiation between OpenVPN server and client success, virtual network adapter which address is 192.168.0.200/24 is created on notebook and some packet belonging to 192.168.0.0/24 is encrypted and goes through virtual network which is written in pink color line at picture above and arrives to 192.168.0.103/24, then packets is decrypted and goes from 192.168.0.103 to some address in 192.18.0.0/24 subnet. This is written in blue line at picture above.
You should use UDP for VPN connection instead of TCP. Please read “Why TCP Over TCP Is A Bad Idea”. Therefore any protocol over ssh is also bad idea because you accumulate using TCP stack as a result. When you use TCP over UDP, UDP act as (maybe lossy) network link and UDP doesn’t care about timeout and retransmission, but TCP does it instead of underling UDP. But some company permits only TCP to go through proxy server. So OpenVPN also supports to use TCP for VPN connection.
3. Environment
Ok. Now let me start to deplyment.
- OpenVPN Server: Scientific Linux 6
- kernel: 2.6.32-131.2.1.el6.x86_64
- openvpn-2.1.4-1.el6.x86_64
- also uses bridge-utils and openssl
- OpenVPN Client: Windows 7
- OpenVPN for Windows
4. How to deploy environment
4.1. install Schientific Linux 6 and OpenVPN package
I’ve installed Scientific Linux 6 into virtual host. Virtual hosts including this OpenVPN server is connected to bridge device and goes through physical ethernet interface. Then I’ve installed openvpn-2.1.4-1.el6.x86_64 using yum command.
# yum install openvpn
Do not forget to disable SELinux and Firewall.
4.2. Create some public/private key pairs
OpenVPN requires some public key certificate/private key pair for mutual authentification. You have to create three pairs at least.
- for CA(Certificate Authority)
- for Server(OpenVPN server)
- for Client(OpenVPN client)
I drew type of certificates and which component should be installed to server and client.
4.2.1. Create your CA’s certificate and private key
Under Scientific Linux 6 environment, you can create your CA’s certificate and private key easy. Red character shows what you should type.
# cd /usr/share/openvpn/easy-rsa/2.0
# . ./vars
# ./clean-all
# ./build-ca
Generating a 1024 bit RSA private key
.................++++++
..++++++
writing new private key to 'ca.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [US]:<your country>
State or Province Name (full name) [CA]:<your province>
Locality Name (eg, city) [SanFrancisco]:<your city>
Organization Name (eg, company) [Fort-Funston]:<your organizaton>
Organizational Unit Name (eg, section) []:
Common Name (eg, your name or your server's hostname) [Fort-Funston CA]:<your hostname>
Name []:
Email Address [me@myhost.mydomain]:
# ls keys
ca.crt ca.key index.txt serial
# cat keys/ca.crt
-----BEGIN CERTIFICATE-----
MIIDezCCAuSgAwIBAgIJAKIB35vl1bhxMA0GCSqGSIb3DQEBBQUAMIGGMQswCQYD
(snip)
ehatRw9UmWMPz+ASZ/VW8M0DXs/TgZd5FAXg7DtP9Q==
-----END CERTIFICATE-----
# cat keys/ca.key
-----BEGIN PRIVATE KEY-----
MIICdgIBADANBgkqhkiG9w0BAQEFAASCAmAwggJcAgEAAoGBALUUl0Uk9mrHhVdH
(snip)
xvndx7Vqja46rg==
-----END PRIVATE KEY-----
#
4.2.2. Create certificate and private key for OpenVPN server
This operation is continuous from 4.2.1.
# ./build-key-server server
Generating a 1024 bit RSA private key
.................++++++
..++++++
writing new private key to 'server.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [US]:<your country>
State or Province Name (full name) [CA]:<your province>
Locality Name (eg, city) [SanFrancisco]:<your city>
Organization Name (eg, company) [Fort-Funston]:<your organizaton>
Organizational Unit Name (eg, section) []:
Common Name (eg, your name or your server's hostname) [Fort-Funston CA]:<your hostname>
Name []:
Email Address [me@myhost.mydomain]:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:<your challenge password, blank is allowed>
An optional company name []:
Using configuration from /usr/share/openvpn/easy-rsa/2.0/openssl.cnf
Check that the request matches the signature
Signature ok
The Subject's Distinguished Name is as follows
countryName : PRINTABLE:'JP'
stateOrProvinceName : PRINTABLE:'Tokyo'
localityName : PRINTABLE:'Shinagawa'
organizationName : PRINTABLE:'mycompany'
commonName : PRINTABLE:'myserver.mydoamin'
emailAddress :IA5STRING:'me@myhost.mydomain'
Certificate is to be certified until Jul 19 12:38:58 2021 GMT (3650 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
# ls keys
01.pem ca.key index.txt.attr serial server.crt server.key
ca.crt index.txt index.txt.old serial.old server.csr
# cat keys/server.crt
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 1 (0x1)
Signature Algorithm: sha1WithRSAEncryption
Issuer: C=JP, ST=Tokyo, L=Shinagawa, O=mycompany, CN=myserver.mydomain/emailAddress=me@myhost.mydomain
Validity
Not Before: Jul 22 12:38:58 2011 GMT
Not After : Jul 19 12:38:58 2021 GMT
Subject: C=JP, ST=Tokyo, L=Shinagawa, O=mycompany, CN=myserver.mydoamin/emailAddress=me@myhost.mydomain
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (1024 bit)
Modulus:
00:d2:38:76:8a:af:4c:c5:fc:94:e9:a0:c6:49:93:
59:ef:16:99:af:8b:e3:8f:69:fa:e4:09:eb:be:c4:
7f:e2:4b:db:cb:f4:64:f1:d9:42:29:9b:3c:ff:8f:
60:60:cf:9c:33:10:51:05:cf:9c:04:fb:da:e3:8f:
5e:a6:7f:11:b4:39:fd:74:75:72:38:20:af:89:f0:
f7:ab:ad:3d:90:21:bd:0e:07:ab:f4:0b:ec:b7:cb:
3e:d8:37:76:86:91:e2:16:c6:92:37:b8:62:16:8e:
ff:9c:87:f9:98:c6:09:a1:7f:bc:28:dc:70:bc:7a:
7b:1e:a4:0c:9b:e7:4b:ba:d9
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Cert Type:
SSL Server
Netscape Comment:
Easy-RSA Generated Server Certificate
X509v3 Subject Key Identifier:
18:9C:4E:40:03:C1:E0:EE:58:D2:C8:D0:78:80:ED:BA:B2:41:03:2E
X509v3 Authority Key Identifier:
keyid:33:B9:D8:5A:98:06:DA:B1:B1:7E:EC:75:C3:85:32:7B:63:7D:71:C1
DirName:/C=JP/ST=Tokyo/L=Shinagawa/O=mycompany/CN=myserver.mydomain/emailAddress=me@myhost.mydomain
serial:A2:01:DF:9B:E5:D5:B8:71
X509v3 Extended Key Usage:
TLS Web Server Authentication
X509v3 Key Usage:
Digital Signature, Key Encipherment
Signature Algorithm: sha1WithRSAEncryption
85:0b:14:5d:03:d7:c0:80:2a:b1:b5:de:60:d0:1f:dc:aa:b6:
b4:0e:f4:c8:8e:3f:0d:90:43:b0:f1:e0:69:cd:d3:4f:40:cf:
76:5f:f4:d6:60:44:ca:49:c9:b5:b0:fa:a4:3f:ba:19:e5:d9:
6e:f2:f5:b3:70:53:0b:be:c4:aa:2c:f2:a5:89:4f:c1:d3:9a:
1c:f5:16:63:f6:ab:b4:0c:36:97:07:a3:a7:99:65:84:36:b1:
03:25:8f:32:ca:54:62:c3:e2:73:e8:ef:19:19:bd:2d:6a:f3:
29:3e:3a:bc:54:b5:45:c8:a7:b0:54:e4:eb:f0:38:f2:0a:b9:
0a:6a
-----BEGIN CERTIFICATE-----
MIID3TCCA0agAwIBAgIBATANBgkqhkiG9w0BAQUFADCBhjELMAkGA1UEBhMCSlAx
(snip)
VGLD4nPo7xkZvS1q8yk+OrxUtUXIp7BU5OvwOPIKuQpq
-----END CERTIFICATE-----
# cat keys/server.key
-----BEGIN PRIVATE KEY-----
MIICeAIBADANBgkqhkiG9w0BAQEFAASCAmIwggJeAgEAAoGBANI4doqvTMX8lOmg
(snip)
bZgJU2uKuRfpVqTd
-----END PRIVATE KEY-----
#
4.2.3. Create certificate and private key for OpenVPN client
This operation is continuous from 4.2.2.
# ./build-key client
Generating a 1024 bit RSA private key
.................++++++
..++++++
writing new private key to 'client.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [US]:<your country>
State or Province Name (full name) [CA]:<your province>
Locality Name (eg, city) [SanFrancisco]:<your city>
Organization Name (eg, company) [Fort-Funston]:<your organizaton>
Organizational Unit Name (eg, section) []:
Common Name (eg, your name or your server's hostname) [Fort-Funston CA]:<your hostname>
Name []:
Email Address [me@myhost.mydomain]:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:<your challenge password, blank is allowed>
An optional company name []:
Using configuration from /usr/share/openvpn/easy-rsa/2.0/openssl.cnf
Check that the request matches the signature
Signature ok
The Subject's Distinguished Name is as follows
countryName : PRINTABLE:'JP'
stateOrProvinceName : PRINTABLE:'Tokyo'
localityName : PRINTABLE:'Shinagawa'
organizationName : PRINTABLE:'mycompany'
commonName : PRINTABLE:'myserver.mydoamin'
emailAddress :IA5STRING:'me@myhost.mydomain'
Certificate is to be certified until Jul 19 12:38:58 2021 GMT (3650 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
# ls keys
01.pem ca.key client.key index.txt.attr.old serial.old server.key
02.pem client.crt index.txt index.txt.old server.crt
ca.crt client.csr index.txt.attr serial server.csr
# cat keys/client.crt
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 2 (0x2)
Signature Algorithm: sha1WithRSAEncryption
Issuer: C=JP, ST=Tokyo, L=Shinagawa, O=mycompany, CN=myserver.mydomain/emailAddress=me@myhost.mydomain
Validity
Not Before: Jul 22 13:03:27 2011 GMT
Not After : Jul 19 13:03:27 2021 GMT
Subject: C=JP, ST=Tokyo, L=Shinagawa, O=mycompany, CN=myclient.mydomain/emailAddress=me@myhost.mydomain
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (1024 bit)
Modulus:
00:c7:55:17:b5:88:8b:9b:64:83:24:f4:fb:80:b7:
67:93:2c:40:e9:cb:96:6e:08:3e:f6:b3:df:06:f4:
8c:e6:ed:f4:90:07:0e:a1:1a:77:50:6e:e1:40:e5:
79:4e:96:08:e4:78:26:59:56:c0:29:27:b0:ed:fd:
1f:3d:6b:63:86:ba:3f:39:04:3c:a5:57:d5:b3:5c:
92:f3:59:6f:10:0e:be:ad:57:ab:aa:3a:34:17:60:
81:69:60:75:73:29:32:ec:84:66:02:53:ff:83:2b:
ad:32:d5:e3:aa:0e:25:ab:c1:95:04:35:db:af:f2:
83:4d:71:a3:d0:55:90:04:7d
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
Easy-RSA Generated Certificate
X509v3 Subject Key Identifier:
CD:13:BC:C7:57:2B:8D:3F:C1:E2:66:A8:5A:7B:47:2D:43:0E:96:DD
X509v3 Authority Key Identifier:
keyid:33:B9:D8:5A:98:06:DA:B1:B1:7E:EC:75:C3:85:32:7B:63:7D:71:C1
DirName:/C=JP/ST=Tokyo/L=Shinagawa/O=mycompany/CN=myserver.mydomain/emailAddress=me@myhost.mydomain
serial:A2:01:DF:9B:E5:D5:B8:71
X509v3 Extended Key Usage:
TLS Web Client Authentication
X509v3 Key Usage:
Digital Signature
Signature Algorithm: sha1WithRSAEncryption
81:3d:3c:21:ad:ff:92:9a:d0:1f:1f:10:26:b8:00:cf:e6:06:
59:20:d9:0d:0e:bf:ba:2c:c3:20:54:32:b6:c3:49:6a:9a:31:
fb:b2:ed:0d:37:90:6b:10:41:71:23:38:f5:d8:ac:dc:39:9e:
97:0d:1f:dd:a8:9e:9e:7c:32:75:91:75:ea:80:76:e2:e6:b4:
51:44:32:d4:a5:9b:e4:28:36:88:34:9c:8a:c5:ee:09:94:f3:
9e:f9:1b:fc:31:df:42:a4:79:17:65:73:4c:d1:d4:cc:76:b3:
a7:fb:4f:b6:dd:c8:86:fb:bc:84:93:db:d1:8e:8c:65:64:a8:
58:93
-----BEGIN CERTIFICATE-----
MIID3TCCA0agAwIBAgIBATANBgkqhkiG9w0BAQUFADCBhjELMAkGA1UEBhMCSlAx
(snip)
joxlZKhYkw==
-----END CERTIFICATE-----
# cat keys/client.key
-----BEGIN PRIVATE KEY-----
MIICdQIBADANBgkqhkiG9w0BAQEFAASCAl8wggJbAgEAAoGBAMdVF7WIi5tkgyT0
(snip)
BBMuuJRvG/fC
-----END PRIVATE KEY-----
#
4.2.4. Generate Diffie-Hellman parameter
For OpenVPN server you have to generate your own Diffie-Hellman parameter.
# cd /usr/share/openvpn/easy-rsa/2.0/
# ./build-dh
Generating DH parameters, 1024 bit long safe prime, generator 2
This is going to take a long time
..............................................................................................................+..............................................................................................+.......................+........................+......+..................+............................................+.........................+..........................+..........................................................+.......................+.................+............................................+................++*++*++*
# ls keys
01.pem ca.key client.key index.txt.attr serial server.csr
02.pem client.crt dh1024.pem index.txt.attr.old serial.old server.key
ca.crt client.csr index.txt index.txt.old server.crt
# cat keys/dh1024.pem
-----BEGIN DH PARAMETERS-----
MIGHAoGBAOn6qlt6EnKXCCKXiA6BPEw0ZWsJbA3+LjSCY6Zn2dBQF48HqvdEDtEF
Mib+p/scL3BdeN11rpQ4/oIMzTgHXitJsahb5wbzlMhjvSyQucKqfjrOVsG/ZOYo
Onzrlty926EluiPNA/PP98UNNQCskXR9pKrc4LTAn99fbujr4E9zAgEC
-----END DH PARAMETERS-----
#
4.3. Create OpenVPN configuration file
By default, there is no file under /etc/openvpn. Refer /usr/share/doc/openvpn/sample-config-files and create your own configuration.
This is configuration file I modified and placed as /etc/openvpn/server.conf. Red charactor is modified.
#################################################
# Sample OpenVPN 2.0 config file for #
# multi-client server. #
# #
# This file is for the server side #
# of a many-clients one-server #
# OpenVPN configuration. #
# #
# OpenVPN also supports #
# single-machine single-machine #
# configurations (See the Examples page #
# on the web site for more info). #
# #
# This config should work on Windows #
# or Linux/BSD systems. Remember on #
# Windows to quote pathnames and use #
# double backslashes, e.g.: #
# "C:\\Program Files\\OpenVPN\\config\\foo.key" #
# #
# Comments are preceded with '#' or ';' #
#################################################
# Which local IP address should OpenVPN
# listen on? (optional)
;local a.b.c.d
# Which TCP/UDP port should OpenVPN listen on?
# If you want to run multiple OpenVPN instances
# on the same machine, use a different port
# number for each one. You will need to
# open up this port on your firewall.
port 1194
# TCP or UDP server?
;proto tcp
proto udp
# "dev tun" will create a routed IP tunnel,
# "dev tap" will create an ethernet tunnel.
# Use "dev tap0" if you are ethernet bridging
# and have precreated a tap0 virtual interface
# and bridged it with your ethernet interface.
# If you want to control access policies
# over the VPN, you must create firewall
# rules for the the TUN/TAP interface.
# On non-Windows systems, you can give
# an explicit unit number, such as tun0.
# On Windows, use "dev-node" for this.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
dev tap0
;dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel if you
# have more than one. On XP SP2 or higher,
# you may need to selectively disable the
# Windows firewall for the TAP adapter.
# Non-Windows systems usually don't need this.
;dev-node MyTap
# SSL/TLS root certificate (ca), certificate
# (cert), and private key (key). Each client
# and the server must have their own cert and
# key file. The server and all clients will
# use the same ca file.
#
# See the "easy-rsa" directory for a series
# of scripts for generating RSA certificates
# and private keys. Remember to use
# a unique Common Name for the server
# and each of the client certificates.
#
# Any X509 key management system can be used.
# OpenVPN can also use a PKCS #12 formatted key file
# (see "pkcs12" directive in man page).
ca /usr/share/openvpn/easy-rsa/2.0/keys/ca.crt
cert /usr/share/openvpn/easy-rsa/2.0/keys/server.crt
key /usr/share/openvpn/easy-rsa/2.0/keys/server.key # This file should be kept secret
# Diffie hellman parameters.
# Generate your own with:
# openssl dhparam -out dh1024.pem 1024
# Substitute 2048 for 1024 if you are using
# 2048 bit keys.
dh /usr/share/openvpn/easy-rsa/2.0/keys/dh1024.pem
# Configure server mode and supply a VPN subnet
# for OpenVPN to draw client addresses from.
# The server will take 10.8.0.1 for itself,
# the rest will be made available to clients.
# Each client will be able to reach the server
# on 10.8.0.1. Comment this line out if you are
# ethernet bridging. See the man page for more info.
;server 10.8.0.0 255.255.255.0
;server 10.8.0.0 255.255.255.0
# Maintain a record of client virtual IP address
# associations in this file. If OpenVPN goes down or
# is restarted, reconnecting clients can be assigned
# the same virtual IP address from the pool that was
# previously assigned.
;ifconfig-pool-persist ipp.txt
# Configure server mode for ethernet bridging.
# You must first use your OS's bridging capability
# to bridge the TAP interface with the ethernet
# NIC interface. Then you must manually set the
# IP/netmask on the bridge interface, here we
# assume 10.8.0.4/255.255.255.0. Finally we
# must set aside an IP range in this subnet
# (start=10.8.0.50 end=10.8.0.100) to allocate
# to connecting clients. Leave this line commented
# out unless you are ethernet bridging.
;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100
server-bridge 192.168.0.103 255.255.255.0 192.168.0.200 192.168.0.210
# Configure server mode for ethernet bridging
# using a DHCP-proxy, where clients talk
# to the OpenVPN server-side DHCP server
# to receive their IP address allocation
# and DNS server addresses. You must first use
# your OS's bridging capability to bridge the TAP
# interface with the ethernet NIC interface.
# Note: this mode only works on clients (such as
# Windows), where the client-side TAP adapter is
# bound to a DHCP client.
;server-bridge
# Push routes to the client to allow it
# to reach other private subnets behind
# the server. Remember that these
# private subnets will also need
# to know to route the OpenVPN client
# address pool (10.8.0.0/255.255.255.0)
# back to the OpenVPN server.
;push "route 192.168.10.0 255.255.255.0"
;push "route 192.168.20.0 255.255.255.0"
push "route 192.168.0.0 255.255.255.0"
# To assign specific IP addresses to specific
# clients or if a connecting client has a private
# subnet behind it that should also have VPN access,
# use the subdirectory "ccd" for client-specific
# configuration files (see man page for more info).
# EXAMPLE: Suppose the client
# having the certificate common name "Thelonious"
# also has a small subnet behind his connecting
# machine, such as 192.168.40.128/255.255.255.248.
# First, uncomment out these lines:
;client-config-dir ccd
;route 192.168.40.128 255.255.255.248
# Then create a file ccd/Thelonious with this line:
# iroute 192.168.40.128 255.255.255.248
# This will allow Thelonious' private subnet to
# access the VPN. This example will only work
# if you are routing, not bridging, i.e. you are
# using "dev tun" and "server" directives.
# EXAMPLE: Suppose you want to give
# Thelonious a fixed VPN IP address of 10.9.0.1.
# First uncomment out these lines:
;client-config-dir ccd
;route 10.9.0.0 255.255.255.252
# Then add this line to ccd/Thelonious:
# ifconfig-push 10.9.0.1 10.9.0.2
# Suppose that you want to enable different
# firewall access policies for different groups
# of clients. There are two methods:
# (1) Run multiple OpenVPN daemons, one for each
# group, and firewall the TUN/TAP interface
# for each group/daemon appropriately.
# (2) (Advanced) Create a script to dynamically
# modify the firewall in response to access
# from different clients. See man
# page for more info on learn-address script.
;learn-address ./script
# If enabled, this directive will configure
# all clients to redirect their default
# network gateway through the VPN, causing
# all IP traffic such as web browsing and
# and DNS lookups to go through the VPN
# (The OpenVPN server machine may need to NAT
# or bridge the TUN/TAP interface to the internet
# in order for this to work properly).
;push "redirect-gateway def1 bypass-dhcp"
# Certain Windows-specific network settings
# can be pushed to clients, such as DNS
# or WINS server addresses. CAVEAT:
# http://openvpn.net/faq.html#dhcpcaveats
# The addresses below refer to the public
# DNS servers provided by opendns.com.
;push "dhcp-option DNS 208.67.222.222"
;push "dhcp-option DNS 208.67.220.220"
# This is DNS server of my home
push "dhcp-option DNS 192.168.0.101"
# Uncomment this directive to allow different
# clients to be able to "see" each other.
# By default, clients will only see the server.
# To force clients to only see the server, you
# will also need to appropriately firewall the
# server's TUN/TAP interface.
client-to-client
# Uncomment this directive if multiple clients
# might connect with the same certificate/key
# files or common names. This is recommended
# only for testing purposes. For production use,
# each client should have its own certificate/key
# pair.
#
# IF YOU HAVE NOT GENERATED INDIVIDUAL
# CERTIFICATE/KEY PAIRS FOR EACH CLIENT,
# EACH HAVING ITS OWN UNIQUE "COMMON NAME",
# UNCOMMENT THIS LINE OUT.
;duplicate-cn
# The keepalive directive causes ping-like
# messages to be sent back and forth over
# the link so that each side knows when
# the other side has gone down.
# Ping every 10 seconds, assume that remote
# peer is down if no ping received during
# a 120 second time period.
keepalive 10 120
# For extra security beyond that provided
# by SSL/TLS, create an "HMAC firewall"
# to help block DoS attacks and UDP port flooding.
#
# Generate with:
# openvpn --genkey --secret ta.key
#
# The server and each client must have
# a copy of this key.
# The second parameter should be '0'
# on the server and '1' on the clients.
;tls-auth ta.key 0 # This file is secret
# Select a cryptographic cipher.
# This config item must be copied to
# the client config file as well.
;cipher BF-CBC # Blowfish (default)
;cipher AES-128-CBC # AES
;cipher DES-EDE3-CBC # Triple-DES
# Enable compression on the VPN link.
# If you enable it here, you must also
# enable it in the client config file.
comp-lzo
# The maximum number of concurrently connected
# clients we want to allow.
;max-clients 100
# It's a good idea to reduce the OpenVPN
# daemon's privileges after initialization.
#
# You can uncomment this out on
# non-Windows systems.
;user nobody
;group nobody
# The persist options will try to avoid
# accessing certain resources on restart
# that may no longer be accessible because
# of the privilege downgrade.
persist-key persist-tun
# Output a short status file showing
# current connections, truncated
# and rewritten every minute.
status /var/log/openvpn-status.log
# By default, log messages will go to the syslog (or
# on Windows, if running as a service, they will go to
# the "\Program Files\OpenVPN\log" directory).
# Use log or log-append to override this default.
# "log" will truncate the log file on OpenVPN startup,
# while "log-append" will append to it. Use one
# or the other (but not both).
log /var/log/openvpn.log
log-append /var/log/openvpn.log
# Set the appropriate level of log
# file verbosity.
#
# 0 is silent, except for fatal errors
# 4 is reasonable for general usage
# 5 and 6 can help to debug connection problems
# 9 is extremely verbose
verb 4
# Silence repeating messages. At most 20
# sequential messages of the same message
# category will be output to the log.
;mute 20
client-cert-not-required
username-as-common-name
# Each user require user name and password
plugin /usr/lib64/openvpn/plugin/lib/openvpn-auth-pam.so login
management localhost 7505
And edit some script to work with OpenVPN.
/etc/openvpn/bridge-start
#!/bin/bash
#################################
# Set up Ethernet bridge on Linux
# Requires: bridge-utils
#################################
# Define Bridge Interface
br="br0"
# Define list of TAP interfaces to be bridged,
# for example tap="tap0 tap1 tap2".
tap="tap0"
# Define physical ethernet interface to be bridged
# with TAP interface(s) above.
eth="eth0"
eth_ip="192.168.0.103"
eth_netmask="255.255.255.0"
eth_broadcast="192.168.0.255"
for t in $tap; do
openvpn --mktun --dev $t
done
brctl addbr $br
brctl addif $br $eth
for t in $tap; do
brctl addif $br $t
done
for t in $tap; do
ifconfig $t 0.0.0.0 promisc up
done
ifconfig $eth 0.0.0.0 promisc up
ifconfig $br $eth_ip netmask $eth_netmask broadcast $eth_broadcast
/etc/openvpn/bridge-stop
#!/bin/bash
####################################
# Tear Down Ethernet bridge on Linux
####################################
# Define Bridge Interface
br="br0"
# Define list of TAP interfaces to be bridged together
tap="tap0"
ifconfig $br down
brctl delbr $br
for t in $tap; do
openvpn --rmtun --dev $t
done
/etc/openvpn/openvpn-startup
#!/bin/sh
/etc/openvpn/bridge-start
/etc/openvpn/openvpn-shutdown
#!/bin/sh
/etc/openvpn/bridge-stop
ifdown eth0
ifup eth0
And modify /etc/init.d/openvpn to work with these scripts.
# Location of openvpn binary
openvpn=""
openvpn_locations="/usr/sbin/openvpn /usr/local/sbin/openvpn"
for location in $openvpn_locations
do
if [ -f "$location" ]
then
openvpn=$location
fi
done
# Lockfile
lock="/var/lock/subsys/openvpn"
# PID directory
piddir="/var/run/openvpn"
# Our working directory
work=/etc/openvpn
# Source function library.
. /etc/rc.d/init.d/functions
# Source networking configuration.
. /etc/sysconfig/network
# Check that networking is up.
if [ ${NETWORKING} = "no" ]
then
echo "Networking is down"
exit 0
fi
# Check that binary exists
if ! [ -f $openvpn ]
then
echo "openvpn binary not found"
exit 0
fi
# See how we were called.
case "$1" in
start)
echo -n $"Starting openvpn: "
/sbin/modprobe tun >/dev/null 2>&1
# From a security perspective, I think it makes
# sense to remove this, and have users who need
# it explictly enable in their --up scripts or
# firewall setups.
#echo 1 > /proc/sys/net/ipv4/ip_forward
# Run startup script, if defined
if [ -f $work/openvpn-startup ]; then
$work/openvpn-startup
fi
if [ ! -d $piddir ]; then
mkdir $piddir
fi
if [ -f $lock ]; then
# we were not shut down correctly
for pidf in `/bin/ls $piddir/*.pid 2>/dev/null`; do
if [ -s $pidf ]; then
kill `cat $pidf` >/dev/null 2>&1
fi
rm -f $pidf
done
rm -f $lock
sleep 2
fi
rm -f $piddir/*.pid
cd $work
# Start every .conf in $work and run .sh if exists
errors=0
successes=0
for c in `/bin/ls *.conf 2>/dev/null`; do
bn=${c%%.conf}
if [ -f "$bn.sh" ]; then
. ./$bn.sh
fi
rm -f $piddir/$bn.pid
# Handle backward compatibility, see Red Hat Bugzilla ID #458594
script_security=''
if [ -z "$( grep '^[[:space:]]*script-security[[:space:]]' $c )" ]; then
script_security="--script-security 2"
fi
$openvpn --daemon --writepid $piddir/$bn.pid --config $c --cd $work $script_security
if [ $? = 0 ]; then
successes=1
else
errors=1
fi
done
if [ $errors = 1 ]; then
failure; echo
else
success; echo
fi
if [ $successes = 1 ]; then
touch $lock
fi
;;
stop)
echo -n $"Shutting down openvpn: "
for pidf in `/bin/ls $piddir/*.pid 2>/dev/null`; do
if [ -s $pidf ]; then
kill `cat $pidf` >/dev/null 2>&1
fi
rm -f $pidf
done
# Run shutdown script, if defined
if [ -f $work/openvpn-shutdown ]; then
$work/openvpn-shutdown
fi
success; echo
rm -f $lock
;;
restart)
$0 stop
sleep 2
$0 start
;;
reload)
if [ -f $lock ]; then
for pidf in `/bin/ls $piddir/*.pid 2>/dev/null`; do
if [ -s $pidf ]; then
kill -HUP `cat $pidf` >/dev/null 2>&1
fi
done
else
echo "openvpn: service not started"
exit 1
fi
;;
reopen)
if [ -f $lock ]; then
for pidf in `/bin/ls $piddir/*.pid 2>/dev/null`; do
if [ -s $pidf ]; then
kill -USR1 `cat $pidf` >/dev/null 2>&1
fi
done
else
echo "openvpn: service not started"
exit 1
fi
;;
condrestart)
if [ -f $lock ]; then
$0 stop
# avoid race
sleep 2
$0 start
fi
;;
status)
if [ -f $lock ]; then
for pidf in `/bin/ls $piddir/*.pid 2>/dev/null`; do
if [ -s $pidf ]; then
kill -USR2 `cat $pidf` >/dev/null 2>&1
fi
done
echo "Status written to /var/log/messages"
else
echo "openvpn: service not started"
exit 1
fi
;;
*)
echo "Usage: openvpn {start|stop|restart|condrestart|reload|reopen|status}"
exit 1
;;
esac
exit 0
4.4. Enable OpenVPN service
Finally, enable and start OpenVPN service.
# chkconfig openvpn on
# service openvpn start
Check /var/log/openvpn.log that initialization sequence has been completed.
Fri Jul 22 23:08:54 2011 us=512618 Initialization Sequence Completed
5. Prepare your Windows OpenVPN client
There is many OpenVPN related project now. You feels that OpenVPN configuration is not easy so you want to use some GUI client and I admit. But as far as I know and after my trial, I can say that there is NO GUI client which treats OpenVPN function correctly including official packages.
The best way you can do about Windows client, you should install and use CUI instead of GUI.
5.1. Download and install OpenVPN Windows binary
From OpenVPN download page, you should download windows binary. After download has completed execute package to install.
5.2. Prepare certificate, private key, and configuration file
At 4.2.3. you’ve created certificate and private key for client. Copy them into “C:¥Program Files(x86)¥OpenVPN¥config”. And copy certificate of CA(ca.crt) to same place(“C:¥Program Files(x86)¥OpenVPN¥config”).
And you have to create configuration file as “C:¥Program Files(x86)¥OpenVPN¥config¥client.ovpn”. Here is my example. Red character is modified. You should edit with editor which can handle LF as line feed code. It may be mistake that it set to CR+LF.
##############################################
# Sample client-side OpenVPN 2.0 config file #
# for connecting to multi-client server. #
# #
# This configuration can be used by multiple #
# clients, however each client should have #
# its own cert and key files. #
# #
# On Windows, you might want to rename this #
# file so it has a .ovpn extension #
##############################################
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
dev tap
;dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote myserver.mydomain 1194
;remote my-server-2 1194
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don't need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
;user nobody
;group nobody
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
# SSL/TLS parms.
# See the server config file for more
# description. It's best to use
# a separate .crt/.key file pair
# for each client. A single ca
# file can be used for all clients.
ca ca.crt
cert client.crt
key client.key
# Verify server certificate by checking
# that the certicate has the nsCertType
# field set to "server". This is an
# important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the nsCertType
# field set to "server". The build-key-server
# script in the easy-rsa folder will do this.
ns-cert-type server
# If a tls-auth key is used on the server
# then every client must also have the key.
;tls-auth ta.key 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
;cipher x
# Enable compression on the VPN link.
# Don't enable this unless it is also
# enabled in the server config file.
comp-lzo
# Set log file verbosity.
verb 3
# Silence repeating messages
;mute 20
And create user name and password file. I created it as “C:¥Program Files(x86)¥OpenVPN¥config¥auth.cfg”. This file is plain text and line 1 should contain user name and line 2 should contain password.
username
password
Finally create batch file to execute OpenVPN connection.
cd C:¥Program Files(x86)¥OpenVPN¥config
openvpn --client --config client.ovpn --remote myserver.mydomain --proto udp --auth-user-pass auth.cfg
If you want to go through sock proxy when you are about to connect, do like this.
cd C:¥Program Files(x86)¥OpenVPN¥config
openvpn --client --config client.ovpn --remote myserver.mydomain --proto udp --socks-proxy socksserver.yourdomain --auth-user-pass auth.cfg
6. Try your OpenVPN connection
Execute command and confirm that your attempt to try is succeed.
Enjoy your broaden home network !